Catalogues
- NFC Tags
- Paper NFC tagsOn Metal NFC tagsTamper proof nfc tagsFPC NFC tagsSpecial NFC tags
- NFC Cards
- Plastic NFC cardsPaper NFC cardsLF RFID cardCPU / JAVA card
- NFC Key fobs
- Epoxy NFC key tagsPlastic NFC key fobs
- NFC Reader writer
- Fixed NFC reader writerHandheld RFID readerUSB token NFC readerLF RFID Reader
- NFC Wristband
- Reusable NFC wristbandsOne-off NFC wristbands
- RFID inlay
- Sheet type RFID inlayRoll type RFID inlay
- RFID Tag
- RFID Laundry TagRFID Asset TagRFID Pallet Tag
- Smart Device
- RFID Smart CabinetRFID Library DeviceRFID TunnelRFID Retail Device
- RFID Security Gate
- RFID gate
- Library RFID Tags
- RFID Book TagRFID Disc Tag
- UHF Tags
- EPC Gen 2 UHF tagJewelry RFID tagTamper Proof UHF tagRFID Windshield TagCable Tie RFID TagRFID garment tagRFID Clothing Hard TagDual frequency RFID tagRFID Medical TagLED UHF TagARC Certified UHF Tag
- UHF Cards
- UHF Smart Card
- UHF Wristband
- RFID Wristbands
- UHF Reader writer
- Fixed UHF ReaderMobile RFID ReaderR2000 UHF readerE Series UHF readerC Series UHF reader
- UHF Antenna
- UHF RFID Antenna
- On metal RFID Tag
- UHF Metal tagCeramic UHF metal tagFlexible UHF Metal TagPCB UHF Metal Tag
- Animal Tag
- RFID ear tagRFID Animal ReaderInjectable RFID tagRFID foot ring tag
- More Recommend
- RFID asset tagRFID screw tagRFID Seal Tag

GEE-KB-5030 Epoxy RFID key tags
Epoxy+ PVC, 50mm x 30 mm, 125 kHz/ 13.56 MHz, NXP Ntag21x, UL, ULC, MF1k/4k, Desfire, EM4100, T5577 chip, 3-10 cm read distance, IEC14443 A& ISO18092 protocol
Download Specification
OverviewSpecificationApplicationsSupport
GEE-KB-5030 is a high performance RFID key tag, which worked at 125 khz or 13.56 mhz with RFID chip embedded. Typical appilcation: access control, transporation ticket

Main features:
• Mini size with customize printing
• Easy for carrying or hanging through its reserved hole
• Fashioned crystal epoxy surface, free of scratch, abrasion, water, dust .
• High performance NXP NFC chips
• Automatic NFC tags manufacturing technology ensured high performance and environment durability of NFC tags
• Heidelberg 4 color offset craft maximized color reproduction
• ISO9001 Quality control system guarantee diamond like quality
• Green material with ROHS and SGS certification

| Physical | |
| Material | Epoxy + PVC |
| Size | 50 mm x 30mm x 4 mm |
| Antenna | Copper coiling |
| Printing | CMYK full color printing |
| Weight | 10 g |
| Packing | 1pcs / poly bag, 100 bag/ box, 5 kg/ ctn |
| RF | |
| Frequency | 125 Khz/ 13.56 Mhz |
| Chip | LF: EM4100, EM4305, T5577, Hi-tags |
| HF: Ntag213/215/ 216, UL, ULC, Mifare 1k/ 4k, NXP ICODE Slix, NXP ICODE Slix-S | |
| Memory Size( Byte) | depended on chips |
| Read distance | 3- 10 cm |
| Rewrite cycles | 10,000 times |
| Data Retention | 10 year |
| Environment | |
| Working condition | -40 ~ 80°C, 5~ 95% RH, no condensation |
| Storage condition | -20 ~ 45°C, 5~ 95% RH, no condensation |
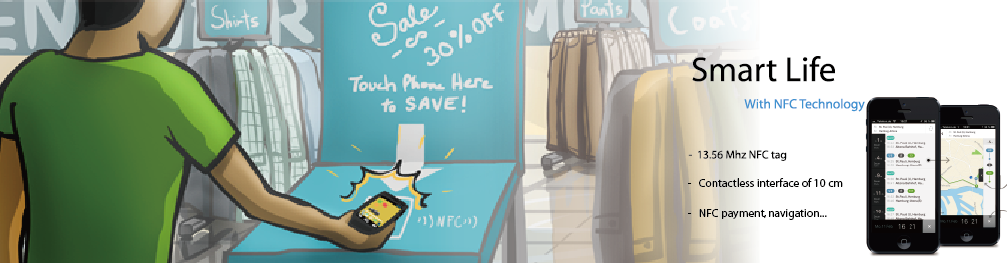
As RFID technology gradually involved in normal life, the usage of RFID technology have greatly change the way we living and bring signifition convenience to us.
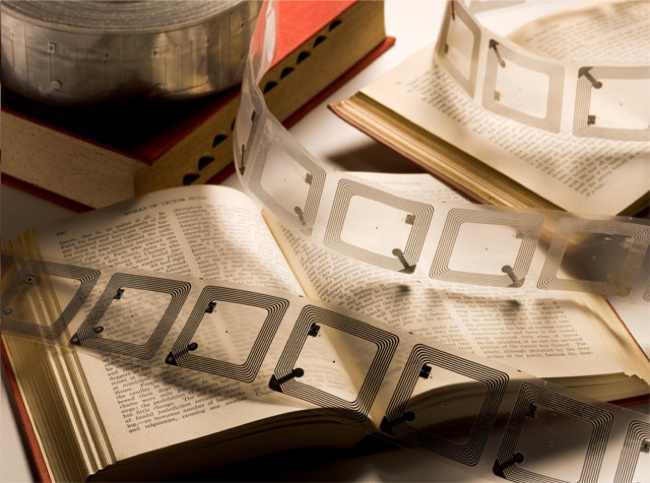
Digit RFID library, which using RFID technology for management and control, was firstly introduced in National Singapore libraries with NXP ICODE Chip for indentifying and tracking, then the trends rapidly expanded into international, nowadays only in China, the number of digit libraries have exceeded over 100.
That is a tremendous achievement since the RFID technology first applied in early 21st century. And there are abundant reasons for RFID libraries completely replaced the traditional ones.
Advantages of RFID Libraries
Rapid check-out / check-in
The use of RFID reduces the amount of time required to perform circulation operations. The most significant time savings are attributable to the facts that information can be read from RFID tags much faster than from barcodes and that several items in a stack can be read at the same time. While initially unreliable, the anti-collision algorithm that allows an entire stack to be check-out or check-in now appears to be working well.
The other time savings realized by circulation staff are modest unless the RFID tags replace both the EM security strips or RF tags of older theft detection systems and the barcodes of the library management system - i.e., the system is a comprehensive RFID system that combines RFID security and the tracking of materials throughout the library; or it is a hybrid system that uses EM for security and RFID for tracking, but handles both simultaneously with a single piece of equipment. There can be as much as a 50 percent increase in throughput. The time savings are less for check-out than for check-in because the time required for check-out usually is extended by social interaction with patrons.
Simplified patron self check-out / check-in
For patrons using self check out, there is a marked improvement because they do not have to carefully place materials within a designated template and they can check out several items at the same time.
Patron self check-in shifts that work from staff to patrons. Staff is relieved further when readers are installed in book-drops.
High reliability
1. The readers are highly reliable. RFID library systems claim an almost 100 percent detection rate using RFID tags.
2. There is no false alarm than with older technologies once an RFID system is properly tuned.
3. RFID systems encode the circulation status on the RFID tag. This is done by designating a bit as the "theft" (EAS) bit and turning it off at time of check-out and on at time of check-in. If the material that has not been properly check-out is taken past the exit sensors, an immediate alarm is triggered.
High-speed inventorying
A unique advantage of RFID systems is their ability to scan books on the shelves without tipping them out or removing them. A hand-held inventory reader can be moved rapidly across a shelf of books to read all of the unique identification information. Using wireless technology, it is possible not only to update the inventory, but also to identify items which are out of proper order.
Automated materials handling
Another application of RFID technology is automated materials handling. This includes conveyer and sorting systems that can move library materials and sort them by category into separate bins or onto separate carts. This significantly reduces the amount of staff time required to ready materials for re-shelving.
Long tag life
Finally, RFID tags last longer than barcodes because nothing comes into contact with them. Most RFID vendors claim a minimum of 100,000 transactions before a tag may need to be replaced.
Related Products
-
GEE-KB-001 RFID key fobs >

ABS enclosure, 45mm x 30mm, LF/ HF/ UHF, 3-10 cm read distance, IEC14443 A
-
GEE-MUT-205 ultrathin metal rfid tag >

50 mm x 26 mm x 1.0 mm, FR4 material, Impinj M4 chip, 4~ 6 meter read distance, IP68
-
GEE-WB-003 Silicone NFC Wristband >

Silicone rubber, 31 mm* 240 mm, adjustable length, 13.56 mhz/ 125 kHz rfid chip, 5 cm read distance, IEC14443 A & ISO15693 protocol
-
GEE-AR-580 134.2 kHz handheld RFID Animal reader >

134.2 kHz, 128 x 32 pixel OLED , 7000 tag storage, FDX-B, HDX, ID64 tag supported, ISO11784/ 85

 NFC Tags
NFC Tags NFC Cards
NFC Cards NFC Key fobs
NFC Key fobs NFC Reader writer
NFC Reader writer NFC Wristband
NFC Wristband RFID inlay
RFID inlay RFID Tag
RFID Tag Smart Device
Smart Device RFID Security Gate
RFID Security Gate Library RFID Tags
Library RFID Tags UHF Tags
UHF Tags UHF Cards
UHF Cards UHF Wristband
UHF Wristband UHF Reader writer
UHF Reader writer UHF Antenna
UHF Antenna On metal RFID Tag
On metal RFID Tag Animal Tag
Animal Tag More Recommend
More Recommend Media & Ads
Media & Ads Transportation & Ticketing
Transportation & Ticketing Library & AssetsManagement
Library & AssetsManagement Logistics & Tracking
Logistics & Tracking Access control
Access control Retail & Gas station
Retail & Gas station Texile solution
Texile solution Health & Medicine
Health & Medicine Food & Wine
Food & Wine Apps for NFC mobile
Apps for NFC mobile Apps for Industry & Retail
Apps for Industry & Retail Manuals
Manuals Software
Software FAQ
FAQ Service Center
Service Center How to choose right tags
How to choose right tags Company news
Company news Industry news
Industry news Technical communication
Technical communication